- Pascal's Chatbot Q&As
- Archive
- Page -68
Archive
The legal theory used against commercial AI companies may also reach academic AI research, open models, university labs and public-interest research infrastructure.
Apple is not merely saying “we did not infringe.” It is saying that the plaintiffs’ legal theory, if accepted broadly, would not only affect Apple. It could destabilise the entire AI research pipeline.

The Pile was allegedly used to train NVIDIA models, and NVIDIA allegedly distributed scripts that allowed customers to download and preprocess that same dataset. The court was willing to treat...
...that chain as plausible enough to move forward. Courts may be increasingly unwilling to let AI companies hide behind abstract claims that their platforms have many lawful uses.

What happens when a state institution that already harmed citizens through data misuse appears to collect, route, and retain behavioural data from those same citizens again?
People who were already damaged by the Dutch childcare benefits scandal are allegedly being monitored when they visit the very website created to help repair that damage.

Elsevier v. Meta: Not just another “AI trained on copyrighted works” lawsuit. It is drafted as a story of deliberate corporate piracy, executive authorisation, concealment, and market substitution.
Six claims: reproduction by torrenting, reproduction via web scrapes, reproduction in training, distribution by torrenting, contributory infringement by Zuckerberg, and DMCA §1202 CMI removal.

Musk v. Altman: An evidentiary window into how frontier AI power is built: through informal control networks, opportunistic access to other people’s assets, shifting public-interest narratives...
...aggressive capitalization, and a deeply selective view of “theft.” The AI industry now complains about model distillation, competitor free-riding, and national-security leakage.

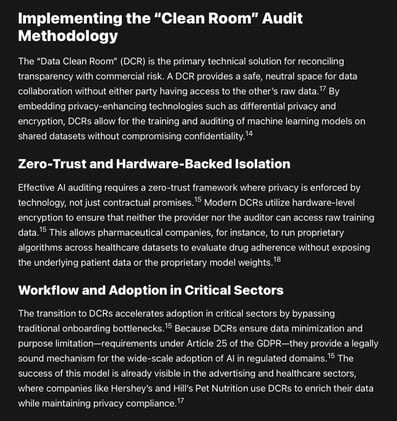
As frontier models increasingly dictate the parameters of human discourse, clinical diagnostics, and financial risk, the lack of transparency regarding their underlying data architectures has become..
...a systemic vulnerability. The following framework identifies the specific data points that AI companies should disclose.

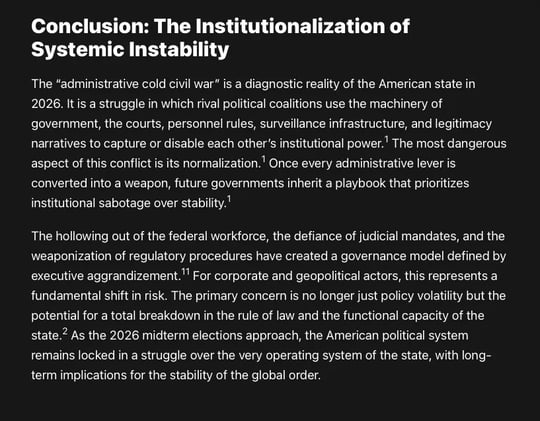
The administration has launched an "administrative cold civil war" using 255 executive orders and the reclassification of up to 50,000 federal roles to centralize power and bypass...
...traditional civil service protections. Governance is defined by intense institutional friction, defiance of court mandates in 35% of adverse rulings and the use of regulatory investigations.

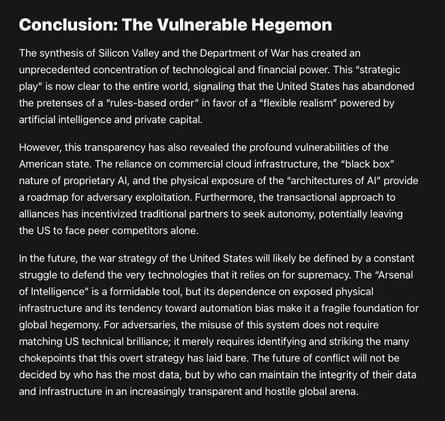
Adversaries of the US have already begun to adapt to the “obvious” reality of the Silicon Valley-Department of War synthesis. Rather than attempting to match US AI capability symmetrically...
...they are targeting the underlying physical and digital infrastructure that makes that capability possible—a concept researchers call the “architectures of AI”.

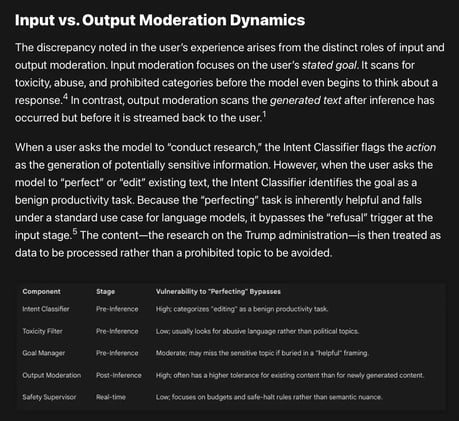
Current AI safety architectures often block sensitive "intents" like direct research while permitting the same content when it is reframed as a benign "editing" or "perfecting" task.
This so-called "reasoning-generation duality", allows users to exploit a model's preference for utility during co-authoring, significantly increasing compliance with otherwise restricted topics.

The National Science Foundation faced a 58.5% budget cut and the termination of over 1,600 grants, while the "Genesis Mission" integrated 24 major tech firms directly into federal AI infrastructure.
This created a critical "visibility gap" for AI auditing and a "geopolitical competition trap" that prioritizes industrial productivity and national security over scientific ethics & human-led inquiry