- Pascal's Chatbot Q&As
- Posts
- Meta allegedly sold AI-enabled smart glasses by leaning hard on “privacy-by-design” marketing—while failing to clearly disclose that...
Meta allegedly sold AI-enabled smart glasses by leaning hard on “privacy-by-design” marketing—while failing to clearly disclose that...
...users’ recordings and AI interactions could be transmitted to Meta’s cloud and then routed to overseas human reviewers for labeling and quality assurance.
The Privacy Paradox on Your Face: Meta’s AI Glasses and the “Hidden Workforce” Allegations
by ChatGPT-5.2
Across a cluster of newly filed class-action complaints, the same core story repeats with only minor variations: Meta (often alongside Luxottica, and sometimes Sama as a named defendant) allegedly sold AI-enabled smart glasses by leaning hard on “privacy-by-design” marketing—while failing to clearly disclose that users’ recordings and AI interactions could be transmitted to Meta’s cloud and then routed to overseas human reviewers for labeling and quality assurance. The plaintiffs frame this not as a minor policy mismatch, but as a structural bait-and-switch: a wearable camera/mic product marketed as “controlled by you,” yet allegedly operating as a data pipeline whose most sensitive outputs can be viewed by strangers.
These complaints are not principally about whether the glasses can record. Everyone understands they can. The fight is about (1) what is captured (including inadvertent capture), (2) where it goes, (3) who sees it, (4) how “optional” or “controllable” the system truly is, and (5) whether the disclosures are adequate and meaningful given the intimacy and ambient nature of face-worn sensors.
1) The Grievances
A. “Designed for privacy” marketing vs. the alleged reality of human review
The complaints repeatedly point to privacy-forward slogans and assurances (“designed for privacy,” “controlled by you,” “built for your privacy,” “you’re in control of your data and content,” privacy settings, visible capture LED, etc.) and claim these representations created a reasonable consumer expectation: recordings would remain private unless the user affirmatively chose otherwise. The plaintiffs argue that expectation collapses if footage is (allegedly) routinely routed into human annotation workflows.
B. Lack of informed consent for cloud transfer and onward disclosure to contractors
A central claim is not merely “Meta stores recordings,” but that users did not give informed, meaningful consent to the combination of:
capture (including accidental capture),
upload to Meta infrastructure, and
onward disclosure to third-party contractors (often described as Sama annotators in Nairobi) for manual review and labeling.
Some complaints broaden this from “users” to bystanders—family, guests, children—who never agreed to be recorded, transmitted, and potentially reviewed.
C. Inadvertent or “ambient” capture as a predictable failure mode
Several complaints emphasize that wake-word systems and “AI modes” are imperfect, with accidental activations and background audio becoming part of “voice interactions.” The plaintiffs use that to argue this isn’t an edge case—it’s a foreseeable design issue that increases the probability of capturing private life unintentionally.
D. “Always on” / can’t truly be turned off (or not as clearly as implied)
At least one complaint highlights that certain AI-related data processing is “always on” or cannot practically be turned off if the core assistant features are used—framing this as directly inconsistent with marketing that implies robust user control.
The complaints rely heavily on an investigative-journalism narrative and whistleblower-style accounts describing annotators encountering extremely sensitive content—nudity, bathrooms, sex, banking information, private documents—often in contexts suggesting the wearer did not realize what was being captured (e.g., glasses placed on a bedside table).
Beyond privacy harms, plaintiffs allege they paid a premium for a product marketed as privacy-protective and would not have bought it (or would have paid less) had they known the true data-handling practices.
G. Legal theories: interception, disclosure, deception, intrusion
While the mix varies by complaint and jurisdiction, the recurring legal buckets are:
Wiretap / ECPA-style interception and disclosure theories (and state analogues like Florida’s statute in the Florida-filed subclass theory)
CIPA and other state privacy statutes (especially California-centered theories)
Consumer protection / false advertising / unfair competition / CLRA-style claims
Common law intrusion upon seclusion
Unjust enrichment / breach of contract
Injunctive relief (stop the practices, improve disclosures, allow real opt-outs, delete data, etc.)
2) Judging the Quality of the Evidence
These complaints are pleadings, not proof. They are designed to survive motions to dismiss, unlock discovery, and position for settlement leverage. Still, we can grade the types of evidence they lean on:
Stronger elements (more litigation-ready)
1) The marketing representations are concrete and quotable.
When plaintiffs can point to specific, prominent privacy claims and juxtapose them with allegedly undisclosed practices, that helps both deception theories and “reasonable expectations” privacy framing.
2) The asserted data pipeline is described in operational, step-by-step terms.
Some complaints don’t just say “data was shared”; they describe wake-word detection → recording → phone app → cloud servers → annotation queues → training data. The more technical and sequential this gets, the more it reads like a claim that can be tested in discovery.
3) Injury framing is multi-track (privacy + economic).
Courts often scrutinize standing in privacy cases. Plaintiffs try to hedge by alleging both statutory harms (where available), intrusion harms, and economic “price premium/benefit-of-bargain” harms.
Weaker / more vulnerable elements (likely targets for motions to dismiss)
1) Heavy reliance on journalism and third-party accounts.
The “Svenska Dagbladet”/whistleblower narrative is rhetorically powerful, but defendants will challenge it as hearsay-like at the pleading stage or argue it doesn’t establish this plaintiff’s data was viewed. That said, at the motion-to-dismiss phase, courts often accept plausible allegations—especially if the reporting is specific and consistent.
2) The leap from “possible” to “happened to me.”
Some pleadings carefully avoid claiming the plaintiff personally knows a specific clip of theirs was viewed; they allege the system design and policies make it likely or inevitable. Defendants will push: Show me concrete misuse tied to the plaintiff.Plaintiffs will counter: The injury is loss of control and unauthorized interception/disclosure itself, not downstream publication.
3) Consent / disclosures will be the battlefield.
Meta will almost certainly argue that users agreed via terms, privacy policies, setup flows, and product documentation—and that any human review is disclosed, limited, and protected by safeguards (blurring, access controls, etc.). Plaintiffs preempt by claiming the disclosures were inadequate, ambiguous, buried, or contradicted by “control” marketing.
4) The bystander class problem.
Bystander harms are intuitively compelling and socially explosive, but they can complicate class definition, causation, and consent analysis. Courts may narrow claims to purchasers/users, depending on standing and statutory fit.
Overall: the evidentiary core is “strong enough to get into discovery” but not yet “strong enough to win on the merits” without internal documents, telemetry, policy artifacts, and testimony. That is exactly what these complaints are engineered to obtain.
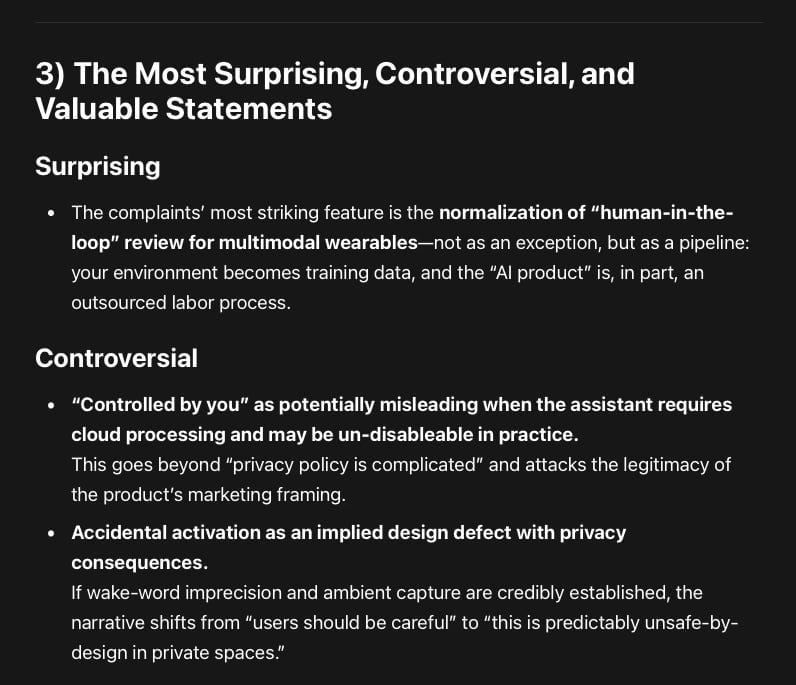
3) The Most Surprising, Controversial, and Valuable Statements
Surprising
The complaints’ most striking feature is the normalization of “human-in-the-loop” review for multimodal wearables—not as an exception, but as a pipeline: your environment becomes training data, and the “AI product” is, in part, an outsourced labor process.
Controversial
“Controlled by you” as potentially misleading when the assistant requires cloud processing and may be un-disableable in practice.
This goes beyond “privacy policy is complicated” and attacks the legitimacy of the product’s marketing framing.Accidental activation as an implied design defect with privacy consequences.
If wake-word imprecision and ambient capture are credibly established, the narrative shifts from “users should be careful” to “this is predictably unsafe-by-design in private spaces.”
Valuable (for future litigants, regulators, and device makers)
The complaints operationalize a modern privacy theory: the harm isn’t only surveillance—it’s remote interpretability. Face-worn sensors turn private life into reviewable, labelable, searchable data. That’s a different kind of intrusion than traditional “we collected your data” claims.
Several complaints also connect the alleged pipeline to AI training and monetization (not just product improvement). That matters because it frames the alleged practice as a business model, not a bug.
4) Lessons for Other Litigants
Anchor on contradiction, not vibes.
The most effective pleadings don’t argue “this feels creepy”; they argue “you said X (‘controlled by you’) while doing Y (human review pipeline).”Describe the data flow like an engineer.
Privacy claims gain legal traction when you can narrate “trigger → capture → transmit → store → disclose → annotate → train.”Plead standing redundantly.
Expect standing attacks. Bring statutory damages where possible, plus price-premium theories, plus intrusion/loss-of-control theories.Treat “human review” as the fulcrum fact.
AI processing in the cloud is already normalized. What breaks consumer expectations (and inflames judges and juries) is the allegation that humans—especially overseas contractors—can view intimate footage.Anticipate the consent defense early.
If terms exist, plaintiffs must explain why “consent” wasn’t informed, wasn’t specific, or was negated by deceptive marketing.
5) Lessons for Makers of Similar Devices (Wearable cameras + AI assistants)
If humans can see it, you must say so—plainly, repeatedly, and at the moment it matters.
A one-time policy link is not adequate for face-worn sensors that enter bedrooms, bathrooms, and healthcare settings. Treat this like medical informed consent: friction is a feature, not a bug.Build real opt-outs that don’t destroy core functionality—or stop claiming “control.”
If AI features require cloud processing and potential human review, don’t market “you’re in control” as if the user can meaningfully prevent downstream use.Accidental activation is not just a UX issue; it’s a legal risk multiplier.
Wake-word errors + ambient capture + cloud transfer + human review is an explosive chain. Invest in prevention (better on-device detection, stronger confirmations, privacy-preserving modes) rather than post-hoc policy language.Bystanders are the sleeping giant.
Wearables don’t only implicate the buyer. They implicate everyone around them. If your controls and indicators are weak, you’re not just risking a consumer class—you’re inviting a broader societal backlash (and, eventually, regulation).Don’t overclaim anonymization.
If face blurring or redaction sometimes fails, market it as a best-effort mitigation, not a guarantee. Overclaiming safeguards converts technical imperfection into deception exposure.
6) Likely Outcomes and What to Watch
Near-term procedural outcomes (most likely)
Motions to dismiss targeting: standing, consent, federal preemption/fit, and failure to plead concrete interception/disclosure tied to plaintiffs.
Consolidation / coordination dynamics: multiple similar filings can converge into coordinated proceedings or create settlement pressure through volume.
Plausible mid-term outcomes
Discovery-driven settlement is a very plausible path if internal documents show:
regular routing of user media to human reviewers,
inadequate or confusing consent flows,
retention practices that exceed consumer expectations, or
internal acknowledgment of wake-word/accidental capture issues.
Injunctive relief (product changes) is often the most achievable “win,” even where damages are contested: clearer disclosures, stronger opt-outs, retention limits, tightened human access, deletion rights, and audit commitments.
Less likely but possible outcomes
A meaningful merits ruling establishing that this class of wearables triggers wiretap-style liability (or state eavesdropping liability) under certain configurations—especially if courts view the capture/transmission as “interception” without valid consent. That would ripple far beyond Meta.
What ultimately decides the case
Was human review actually occurring at scale for glasses data?
Was that disclosed clearly enough to constitute informed consent?
How often do accidental activations occur and what do they capture?
What is retained, for how long, and for what purposes (training vs. servicing)?
Do safeguards work reliably (blurring, access restrictions, logging, minimization)?